Account Data Review – 5548556394, 1839.6370.1637, Efmayasoci, Verccomicsporno, e5b1h1k
The account data review for identifiers 5548556394, 1839.6370.1637, Efmayasoci, Verccomicsporno, and e5b1h1k examines governance, privacy controls, and data minimization in a structured framework. It maps digital records to real-world accounts while preserving privacy through protective identifiers. The analysis focuses on access transparency, consent management, and audit trails, highlighting gaps and corrective actions. The discussion closes with a disciplined rationale for strengthened controls, inviting continued examination of safeguards and accountability mechanisms.
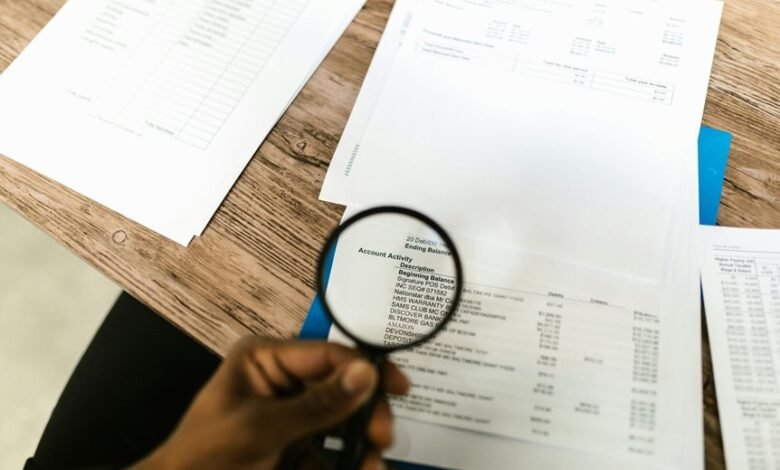
What the Account Data Review Covers
The Account Data Review covers the scope, objectives, and methodologies used to assess account-related information. The analysis delineates privacy controls, data minimization, access transparency, and consent management as core components. It evaluates procedural rigor, audit trails, and compliance benchmarks, emphasizing freedom through responsible governance. Findings identify gaps, propose corrective actions, and ensure ongoing accountability without encroaching on user autonomy.
How Identifiers Map to Real-World Accounts
Identifiers serve as the bridge between digital records and their real-world counterparts, enabling precise mapping without exposing sensitive content. This process highlights systematic linking mechanisms that preserve traceability while respecting boundaries.
The examination emphasizes privacy controls, data minimization, access governance, and consent verification, ensuring accountability, auditable trails, and disciplined data handling.
Clear protocols support controlled exposures, minimizing risk and promoting informed freedom in data ecosystems.
Privacy, Consent, and Access Controls in Practice
What are the practical steps that organizations take to enforce privacy, consent, and access controls in daily data operations, and how are these steps monitored for effectiveness?
The analysis outlines rigorous privacy safeguards, explicit consent mechanisms, and layered access controls integrated with governance practices.
Monitoring emphasizes audit trails, continuous verification, risk assessments, and corrective actions to sustain data integrity and user autonomy.
Practical Data Governance: Safeguards and Best Practices
Practical Data Governance: Safeguards and Best Practices builds on established privacy, consent, and access controls by translating policy into repeatable, operational safeguards. The approach emphasizes systematic implementation, documentation, and monitoring to reduce risk. It delineates data ownership roles, stewardship responsibilities, and accountability metrics. An explicit access taxonomy clarifies who can retrieve data, supporting enforceable controls and responsible use.
Frequently Asked Questions
How Is Data Anonymization Validated Across Platforms?
Data anonymization validation across platforms is assessed through controlled re-identification tests, cross-dataset linkage checks, and privacy impact analyses; emphasis on data minimization and correlation risk informs thresholding, algorithmic randomness, and auditability for transparent, freedom-respecting governance.
What Third-Party Data Sources Are Used for Verification?
Third party data sources are utilized for verification, enabling independent data validation. The process prioritizes data anonymization and compliance testing, ensuring privacy protections while assessing source reliability; methodologies emphasize transparency and robust auditing within an freedom-oriented analytical framework.
How Often Are Access Control Logs Reviewed?
Like clockwork, access control logs are reviewed monthly to ensure timely anomaly detection. This process supports data retention and access monitoring policies, maintaining rigorous governance while preserving user freedoms and accountability within established compliance frameworks.
What Remediation Steps Exist for Data Breach Incidents?
Remediation steps for a data breach include immediate containment, root-cause analysis, and stakeholder notification, followed by data anonymization, vulnerability remediation, and enhanced monitoring. Data breach responses emphasize reproducibility, documentation, and continuous improvement for future resilience.
How Is User Consent Documented for Data Sharing?
Consent documentation records user approvals for data sharing, detailing scope, duration, and purposes. It supports data anonymization and cross platform validation, ensuring transparent consent trails and verifiable authorizations while preserving user autonomy and governance oversight.
Conclusion
The review concludes that the governance framework effectively balances informed freedom with responsible control, leveraging precise data minimization, transparent access logs, and auditable trails. Identifiers map to real-world accounts with clear privacy protections and consent management. Gaps are identified, with corrective actions prioritized to strengthen accountability and oversight. While the methodology is rigorous and documentation is meticulous, modernization—incorporating machine-assisted anomaly detection—could further enhance resilience. In sum, governance remains robust, albeit retrofitted for a future-ready landscape. Deja vu notwithstanding, the dossier insists on adaptability.





