Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
Account data reviews illuminate how identifiers like 8285431493, mez68436136, 9173980781, 7804091305, and 111.90.150.204l function as placeholders whose meaning depends on explicit mapping and traceability. A skeptical lens highlights governance gaps, ownership clarity, and validated provenance to prevent incomplete records from propagating across systems. Linking traceability, access controls, and continuous monitoring can improve reliability and decision support, but the path requires careful scrutiny before proceeding. What concrete steps will move this forward?
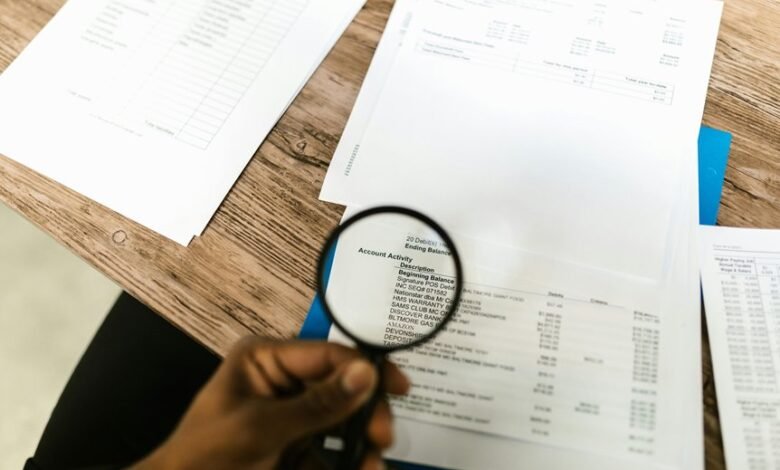
Why Account Data Reviews Matter in Modern MDM
Account data reviews are essential in modern master data management (MDM) because incomplete or inconsistent account records can propagate errors across integrated systems, undermining data reliability and decision-making.
The analysis remains skeptical, noting governance gaps and latent inconsistencies.
Subtopic idea 1, Subtopic idea 2, when addressed, clarify ownership and validation processes, supporting freedom through disciplined data stewardship and proactive discrepancy detection.
Mapping Identifiers: What 8285431493, mez68436136, 9173980781, 7804091305, and 111.90.150.204 Represent
Mapping identifiers such as 8285431493, mez68436136, 9173980781, 7804091305, and 111.90.150.204 requires a careful disentangling of their origins, formats, and intended domains. This analysis treats them as placeholders within data ecosystems, not intrinsic truths. The claim of robustness rests on clear identifiers mapping and vigilant data traceability, ensuring accountability without surrendering intellectual liberty.
A Practical Audit Framework for Traces Across Systems
What constitutes a practical audit framework for traces across systems, and how can it be applied without compromising performance or governance? The framework dissects traceability into governance, data lineage, and access controls, emphasizing minimal overhead. It identifies ownership and securing access, demands verifiable provenance, and continuous monitoring. Skeptical evaluation reveals trade-offs, urging modular deployment and auditable metrics for accountable, freedom-aligned resilience.
Preventing Leaks and Misuse: Best Practices and Next Steps
Preventing leaks and misuse requires a disciplined synthesis of preventative controls, monitoring, and response readiness, grounded in concrete risk assessment rather than aspirational policy.
The analysis emphasizes data governance and data minimization as foundational, with rigorous access controls and clearly defined incident response procedures.
Skeptical evaluation urges continuous improvement, transparency, and disciplined experimentation to deter misuse while preserving legitimate freedom and innovation.
Frequently Asked Questions
How Are Permissions Tied to Each Identifier Across Systems?
Permissions are mapped via a structured permissions mapping, aligning identifiers to cross system roles and access privileges; inconsistencies or gaps reveal integration flaws and drift. Analysts scrutinize cross system roles for coherent enforcement and risk exposure.
Can Identifiers Expire or Be Retired Without Data Loss?
Identifiers can expire or be retired without data loss, provided governance ensures retention of metadata and references. Expired identifiers prompt renewal or reassignment, while retired identifiers require archival support; skeptical review confirms no indirect data exposure from legacy mappings.
What Risks Arise From Overlapping Identifiers Across Platforms?
Could overlapping identifiers across platforms enable unseen links between profiles? They present risks of identity theft, data leakage, and privacy policy gaps, demanding rigorous cross platform mapping, skepticism, and freedom‑loving scrutiny by responsible actors to mitigate exposure.
How Is User Consent Reflected in Audit Trails?
Consent timing is reflected through documented approvals in audit trails; audit ownership clarifies accountability, while data remediation and policy exceptions are noted when deviations occur, enabling skeptical, meticulous evaluation by readers seeking regulatory freedom.
What Are Common False Positives in Data Reconciliation?
False positives in data reconciliation often arise from over-reliance on data normalization and rigid mismatch thresholds; anomaly detection may flag legitimate variance, revealing systemic process flaws, thus provoking skepticism about automated reconciliation and the need for human review.
Conclusion
In the ledger of governance, identifiers act as quiet symbols: placeholders whose meanings drift without traceability. The audit becomes a compass, revealing gaps, ownership vacuums, and provenance fractures. When mapping and access controls align, the system becomes a lighthouse, not a foghorn—guiding decisions with disciplined clarity. Absent that alignment, records propagate like shadows, fragile and misleading. A vigilant, continuous framework is the anchor that prevents leakage, preserving trust and intellectual integrity across landscapes of data.





